Expressvpn Glossary
Threat actor
What is a threat actor?
A threat actor is a person or organized group that intentionally carries out malicious activity against systems, networks, or data.
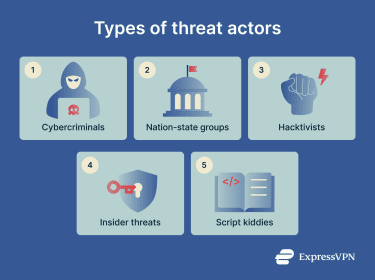
Types of threat actors
Threat actors come in many forms, each with distinct capabilities, motivations, and targets:
- Cybercriminals: Pursue financial gain through scams, ransomware, and data theft.
- Nation-state groups: Conduct espionage or sabotage in support of geopolitical objectives.
- Hacktivists: Disrupt services or leak data to advance an ideological or political cause.
- Insider threats: Misuse legitimate access, intentionally or negligently, to expose data or weaken security.
- Script kiddies: Use existing tools and exploits with limited technical skill, often opportunistically.
How threat actors operate
Threat actors often follow a sequence of steps when carrying out an attack. These patterns are documented in frameworks such as the Cyber Kill Chain and MITRE ATT&CKⓇ, and although no two attacks are identical, many follow this general flow:
- Reconnaissance: The attacker researches the target, identifying employees, systems, and potential weaknesses before making a move.
- Initial access: The attacker gains entry through phishing, software exploits, or stolen credentials, then establishes a foothold to maintain continued access.
- Privilege escalation and lateral movement: The attacker expands permissions and moves across systems to reach higher-value assets.
- Execution: The attacker carries out their end goal, which can include exfiltrating data, deploying malware, disrupting operations, or extorting payment via ransomware.
Where threat actor analysis is applied
Security teams may use the following approaches to identify actor profiles and risk levels:
- Incident response and attribution: Link indicators, behaviors, and timelines to likely actor profiles.
- Threat intelligence and security operations center (SOC) monitoring: Use observed techniques to inform detection and monitoring.
- Security awareness training scenarios: Model realistic phishing and credential abuse patterns based on common actor playbooks.
- Risk management and compliance work: Prioritize controls around the most likely actor types and business impacts.
- Vendor security and third-party reviews: Assess exposure created by partners, suppliers, and shared tooling.
Key privacy and security implications
When threat actors succeed, the impact extends beyond the organization. Employees, customers, and third parties can suffer data exposure, identity theft, and financial or reputational harm.
Regulated industries face additional consequences since a breach can trigger mandatory notifications, regulatory fines, and legal liability depending on the data involved and the jurisdiction.
Further reading
- What is cyber threat hunting, and how does it work?
- What is a honeypot in cybersecurity?
- What is open-source intelligence (OSINT)?
- EternalBlue explained: What it is and how to stay safe
- Signs that your phone screen is hacked, and how to fix it


