Expressvpn Glossary
Stream cipher
What is a stream cipher?
A stream cipher is a type of symmetric encryption that secures data one bit or byte at a time instead of in fixed-size blocks. It generates a pseudorandom keystream and combines it with the plaintext to create ciphertext.
Stream ciphers are designed for speed and low delay, making them suitable for protecting data that’s transmitted in real time. They're commonly used in network security and other applications that handle continuous streams of data.
How does a stream cipher work?
A stream cipher follows a clear sequence from input to encryption and back to decryption.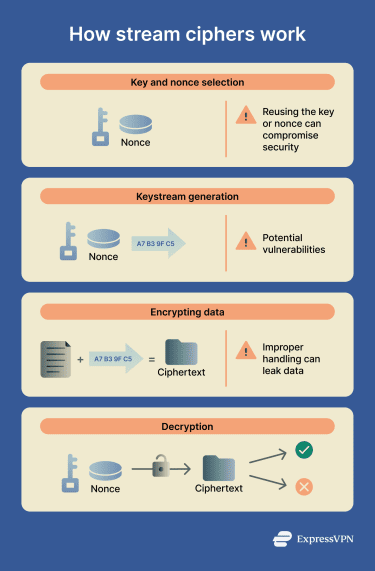
- Secret key and nonce selection: A shared secret key is generated, along with a unique initialization vector or nonce (numbers used once). The nonce must not be reused with the same key because it ensures a different keystream for each encryption.
- Cipher initialization: The key and nonce are provided to the stream-cipher algorithm. This prepares the cipher to produce the keystream used for encryption.
- Keystream generation: After initialization, the cipher produces a pseudorandom sequence of bytes known as the keystream.
- Plaintext encryption: The plaintext is combined with the keystream to produce the ciphertext. It can then be stored or transmitted, usually together with the nonce.
- Ciphertext decryption: The same key and nonce are used to regenerate the keystream. Combining it with the ciphertext restores the original plaintext.
Types of stream ciphers
Stream ciphers are generally divided into two primary categories:
| Type of stream cipher | How the keystream is generated | Synchronization behavior |
| Synchronous stream cipher | Generated independently of the plaintext and ciphertext | Sender and receiver must stay aligned to the same keystream position |
| Self-synchronizing stream cipher | Generated using a fixed number of previous ciphertext bits | Automatically resynchronizes after a short period |
Where are stream ciphers used?
Stream ciphers are used when data must be transmitted continuously and encrypted with minimal delay. They’re common in virtual private networks (VPNs), wireless and cellular communications, and real-time services like online gaming, video streaming, and voice/video messaging.
Many Internet of Things (IoT) devices also rely on stream ciphers, as they operate efficiently on hardware with limited processing power and memory.
Examples of stream ciphers
- Salsa20: A high-speed modern stream cipher designed for software efficiency.
- ChaCha20: A widely used modern stream cipher that improves on Salsa20 and is commonly deployed in Transport Layer Security (TLS), VPNs, and secure messaging.
- RC4: A once-popular cipher that’s now considered obsolete due to security weaknesses.
Stream cipher benefits
Stream ciphers are known to be efficient when handling real-time encrypted traffic, making them suitable for:
- Resource-constrained devices.
- Fast encryption of streaming audio and video.
- Smaller data sizes, since no fixed block size is required.
Stream cipher vulnerabilities
Although stream ciphers can be highly secure, their safety depends on correct implementation:
- Reusing the same keystream with the same key and nonce compromises the plaintext.
- Mishandling nonces/initialization vectors can reveal patterns between encrypted messages.
- Weak software or hardware implementations can leak sensitive data through side-channel attacks, such as timing or power analysis.
Further reading
- What is ChaCha20, and how does it work?
- Symmetric vs. asymmetric encryption: What’s the difference
- Encryption protocols explained: What they are and how they work
- What is TLS encryption, and how does it protect your data?


