Expressvpn Glossary
Infrastructure security
What is infrastructure security?
Infrastructure security is the practice of protecting infrastructure from both physical and digital risks. It safeguards the critical systems and services organizations rely on, including hardware, software, networks, facilities, and data.
How does infrastructure security work?
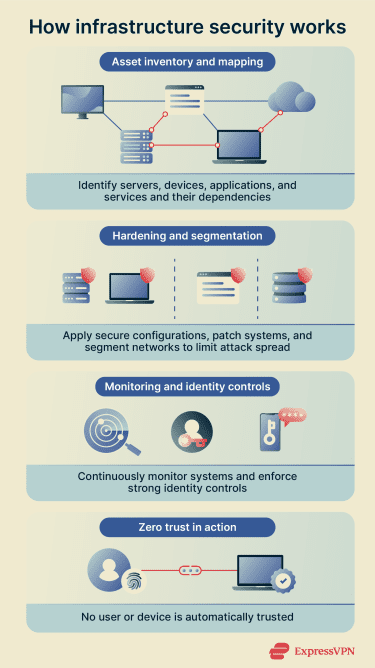 Infrastructure security starts with creating a complete inventory of all assets. This includes servers, devices, applications, and services, and mapping how they depend on each other to identify critical paths and potential points of failure.
Infrastructure security starts with creating a complete inventory of all assets. This includes servers, devices, applications, and services, and mapping how they depend on each other to identify critical paths and potential points of failure.
Systems are then hardened by applying secure configurations and standardized security frameworks, removing unnecessary features, and keeping software and firmware up to date through timely patching. Network segmentation further isolates parts of the environment to limit how far an attacker can move if a breach occurs.
This is then followed by continuous monitoring, suspicious activity detection, and strong identity controls like multi-factor authentication (MFA) to help prevent unauthorized use. These practices are often applied within a zero-trust model, where no user, device, or workload is automatically trusted.
Types of infrastructure security
Infrastructure security spans several domains, each responsible for protecting a different layer of the environment.
- Physical security: Protects facilities, server rooms, hardware, and environmental systems with controlled access, monitoring, and resilience against theft, vandalism, and power or cooling failures.
- Network security: Secures connectivity through segmentation, firewalls, and controlled routing to isolate sensitive systems and restrict unauthorized traffic.
- Cloud security: Safeguards cloud-based infrastructure and the information it processes using strong Identity and Access Management (IAM), encryption, and cloud access security brokers (CASBs).
- Endpoint security: Reduces the risk of compromise by hardening servers and user devices, patching vulnerabilities, and using endpoint detection and response (EDR) tools.
- Security operations: Supports data protection and recovery through governance practices such as change management, backups, and disaster recovery planning.
Where is infrastructure security used?
Infrastructure security is used wherever core systems and digital services must remain reliable and protected. In enterprise IT, it secures internal networks, directory services, and business-critical servers. In cloud environments, it protects virtual machines, containers, and orchestration platforms that run modern applications.
It’s also essential for internet-facing services such as web applications and APIs, where direct exposure to external traffic increases risks. Finally, in critical infrastructure sectors such as utilities, healthcare, and financial services, infrastructure security helps maintain the availability and safety of essential services.
Benefits of infrastructure security
Effective infrastructure security strengthens an organization’s overall resilience. Isolating systems and enforcing access controls limits lateral movement within the environment. This containment reduces the scope of potential breaches and helps prevent widespread business and organizational disruption.
Security and privacy considerations
Infrastructure security introduces important privacy and governance considerations that organizations must manage carefully:
- Telemetry and monitoring: Systems generate large volumes of data that can reveal user behavior or operational patterns if not properly protected.
- Centralized logging: Logs may contain sensitive information and require strict access controls and retention policies.
- Third-party tools: Using vendor security or management tools can expand the trust boundary and increase exposure if the provider is compromised.
- Misconfigurations: Errors in setup or configuration, especially in complex cloud environments, create hidden security gaps.
- Excessive privileges: Overprivileged accounts increase the potential impact of a breach, highlighting the need for strong access governance.
Further reading
- Zero-trust architecture: What it is, how it works, and why it matters
- 7 pillars of zero-trust security, mapped to NIST and DoD
- Internet infrastructure: What it is and how it works
- What is access control? How it works and why it matters


