Expressvpn Glossary
Digital trust
What is digital trust?
Digital trust refers to the level of confidence in the security, reliability, and integrity of digital systems, services, and data. It describes how safe and dependable digital environments are considered for storing information, carrying out transactions, and communicating.
Key dimensions of digital trust
The core elements of digital trust for confidence in digital systems include:
- Security: Protection of systems, networks, and data from unauthorized access or misuse.
- Privacy: Proper handling and protection of personal and sensitive information.
- Transparency: Clear communication about how systems operate and how data is used.
- Accountability: Responsibility for digital practices, including oversight and compliance.
- Reliability and resilience: Consistent system performance and the ability to recover from failures or incidents.
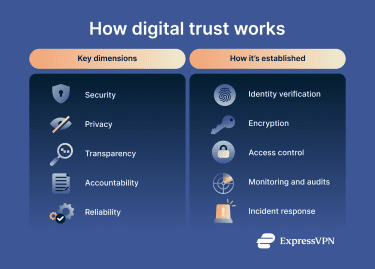
How is digital trust established?
Organizations establish digital trust through technical and organizational controls that protect systems and data and demonstrate accountability.
Common methods include verifying identities through authentication mechanisms, protecting information with encryption and access controls, and ensuring data integrity through cryptographic techniques such as hashes and digital signatures. Continuous monitoring, security audits, and incident response processes also add to it by helping detect misuse and maintain system reliability.
What is the purpose of digital trust?
Digital trust describes the confidence in digital systems to operate securely, reliably, and transparently. It influences how organizations, systems, and users interact in digital environments.
Digital trust relates to:
- Identity and device verification.
- Secure digital transactions and data exchange.
- Organizational accountability and governance.
- Compliance with data protection and privacy requirements.
Where digital trust is applied
Digital trust is applied in systems and services that handle sensitive data, verify identities, or support critical transactions. Common areas include online banking and e-commerce systems, where it secures financial transactions; healthcare platforms, where it protects patient records; and government digital services, where it supports digital identity and secure data handling.
Common ways digital trust can be weakened
Digital trust can be weakened by security failures, weak controls, or practices that compromise privacy and transparency. Key risks include:
- Data breaches: Unauthorized access to sensitive or personal information, often resulting from security vulnerabilities or cyberattacks.
- Weak identity verification: Insufficient authentication processes that fail to confirm a user’s identity, enabling account takeover, impersonation, or unauthorized access.
- Tracking and profiling: Extensive collection and analysis of user behavior that may occur without clear awareness or consent, raising privacy concerns.
- Supply-chain attacks: Security compromises affecting third-party vendors or service providers, allowing attackers to gain indirect access to trusted systems or data.
- Manipulative consent practices (dark patterns): Interface designs that mislead or pressure users into agreeing to data collection or sharing, limiting informed consent.
Further reading
- What is a certificate authority, and how does it work?
- What is TLS encryption, and how does it protect your data?
- SSL vs. TLS: Key differences and why TLS is better
- HTTP vs. HTTPS: How to choose the secure option for your site
- What is OIDC? A complete guide to understanding the identity layer
- Is ID.me safe? A complete guide to digital identity protection


