Expressvpn Glossary
Cybersecurity framework

What is a cybersecurity framework?
A cybersecurity framework is a structured set of standards, guidelines, and practices that an organization uses to organize and manage its cybersecurity activities.
Its core purpose is to provide a consistent, risk-based approach (and common language) for identifying, assessing, prioritizing, and managing cybersecurity risk so security efforts can be planned, implemented, and improved over time.
How does a cybersecurity framework work?
A cybersecurity framework works by giving an organization a standard structure for describing cybersecurity goals, risks, and desired outcomes, then using that structure to assess the current state and plan improvements.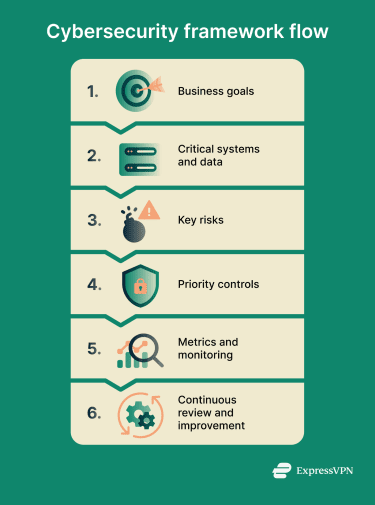 In practice, organizations map existing policies and controls to the framework, identify gaps, prioritize actions based on risk and business needs, and update the program as conditions change. Some frameworks, such as the National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF), also use concepts such as Current Profiles and Target Profiles to compare the current state with a desired future state.
In practice, organizations map existing policies and controls to the framework, identify gaps, prioritize actions based on risk and business needs, and update the program as conditions change. Some frameworks, such as the National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF), also use concepts such as Current Profiles and Target Profiles to compare the current state with a desired future state.
Why is a cybersecurity framework important?
A cybersecurity framework helps organizations manage cybersecurity risk and systematically improve their security practices.
- Reduced likelihood and impact of incidents: A structured, risk-based approach helps select and prioritize safeguards and response capabilities that lower exposure and limit consequences.
- Shared language for risk discussions: Standard outcomes and framework terminology can make cybersecurity posture and priorities easier to communicate across technical and executive audiences.
- Prioritized spending and effort: Gap analysis and risk-based planning help organizations decide what to do first based on risk and mission needs, rather than treating all issues equally.
- Accountability and reporting: Documented objectives, action plans, and progress tracking can support governance, internal reporting, and readiness for audits or assessments. The exact documentation approach depends on the framework used.
- Third‑party oversight: Frameworks can help organizations define and communicate cybersecurity expectations for suppliers and other external partners, although the specific mechanisms vary by framework and program design.
Where is a cybersecurity framework used?
Cybersecurity frameworks are used by organizations of all sizes across industry, government, academia, and non-profits to structure and scale security programs and to help set clear priorities for smaller teams.
Cybersecurity frameworks are used across both IT and, in many cases, operational technology environments, including cloud migrations and hybrid deployments. They can also be scoped to specific systems, services, or business functions, and may support activities such as vendor risk reviews, procurement, incident response, and resilience planning.
In frameworks such as the NIST CSF, functions like Detect, Respond, and Recover help organize those activities.
Limitations and common pitfalls
Cybersecurity frameworks have practical limits, and implementation can fail when common issues are not addressed. Common pitfalls include:
- Checkbox compliance: Treating framework outcomes as a fixed checklist rather than aligning them with organizational goals and risk can weaken results.
- Poor scoping: Vague or inconsistent scope, priorities, or target outcomes can misdirect time, effort, and spending.
- Incomplete inventory: Missing inventories of assets, data, dependencies, or key suppliers make prioritization unreliable, including when legacy or overlooked systems still create risk.
- Irrelevant metrics: Metrics not tied to mission objectives or risk provide limited value and can distract from meaningful improvement.
- Lack of executive support: Without leadership involvement, governance, accountability, and sustained implementation are often inconsistent.
Further reading
- Understanding the NIST Cybersecurity Framework
- What is cybersecurity? A simple guide for beginners
- The ultimate guide to cybersecurity defense
- Cybersecurity vulnerabilities explained
- What is a cybersecurity risk assessment and how does it work?


